Remote Access Overview
What is Remote Access?
Remote Access is an addition to Admin By Request Server Edition that will allow you to connect remotely to your servers and network endpoints directly from your browser, using a lot of the well-known Admin By Request features like: inventory, auditlog, settings and sub-settings, approval flows, integrations etc.
The implementation of Remote Access eliminates the need for VPN and jump servers, while still maintaining a secure and segregated setup.
Prerequisites
Remote Access has two primary ways of operating (i.e. two possible setups):
-
Used as a managed cloud service via Admin By Request.
-
Used as a self-hosted implementation inside your own infrastructure via Docker.
The prerequisites for the Remote Access product vary depending on the desired setup.
1. Remote Access as a managed service
The only requirement for using Remote Access as a managed service is that your infrastructure allows an outbound connection to establish a secure tunnel from your respective endpoints and that these have the Admin By Request Server agent installed.
2. Remote Access as a self-hosted implementation
In order to run Remote Access on-premise inside your own infrastructure, you will need to be able to run a few Docker containers as well as allow outbound connections to Cloudflare in order to establish a tunnel.
How does Remote Access work?
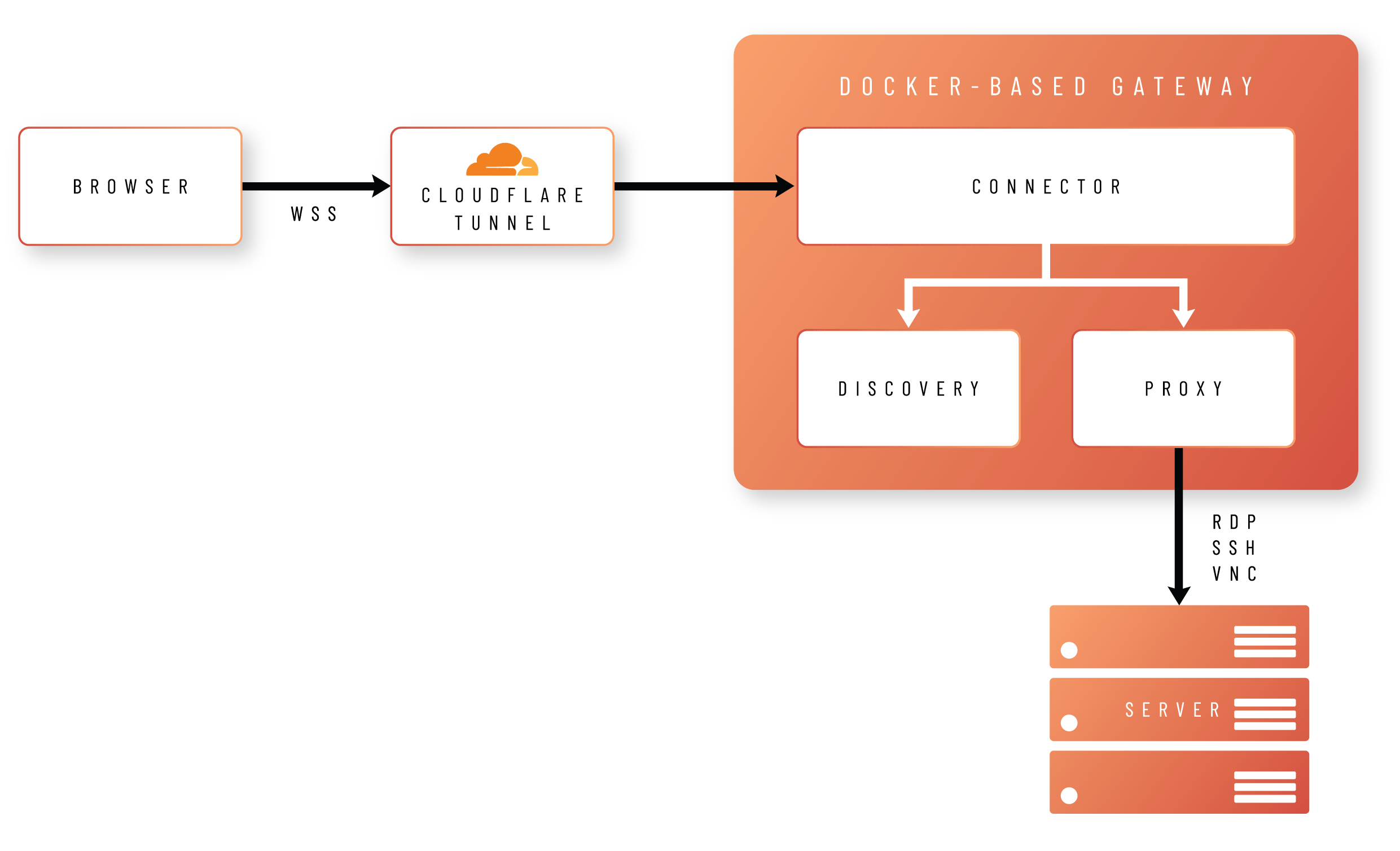
The idea behind Remote Access is to allow users to connect to your remote endpoints using nothing but their browsers. In order to achieve this, the browser creates a Secure WebSocket connection to a Docker-based gateway, hosted either in your own infrastructure or as a managed service.
The gateway comprises three different images:
-
Connector
Handles validation and translation of the data between the portal and the proxy container, as well as managing logs, health checks and other data. -
Proxy
Establishes a protocol connection between Admin By Request and your endpoint using either RDP, SSH or VNC. -
Discovery
Handles automatic discovery of connectable devices running on the same network as the gateway.
What next?
As well as outlining how to get started with each of the two ways of operating Remote Access, this
The next section covers the initial steps for enabling Remote Access, followed by the steps required for a managed cloud service, and then the steps required for a self-hosted implementation.