Malware Detection
What is it?
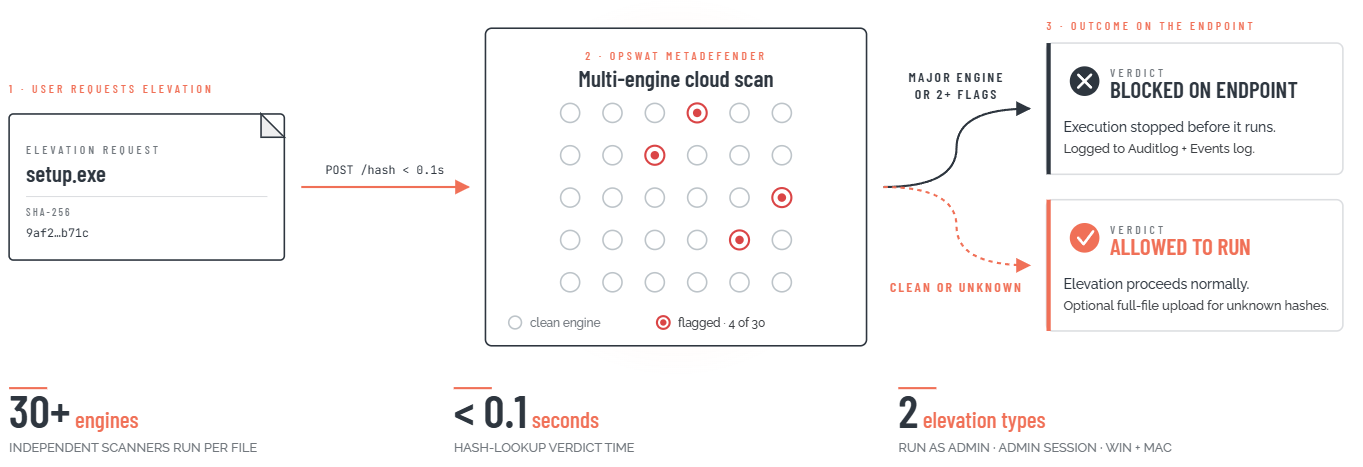
*Malware detection* is a real-time file scanning capability built into Admin By Request (ABR) that intercepts every elevation request and checks the target file against the OPSWAT MetaDefender multi-engine threat database before it is ever executed.
When a user requests to run a file with administrative privileges, ABR sends the file's SHA-256 checksum to MetaDefender's cloud service in under 0.1 seconds. If any major scanning engine - or more than one engine of any kind - flags the file as malicious, execution is blocked on the endpoint before the file does any damage, and the event is recorded in both the Auditlog and the Events log.
For files whose checksums are not yet in MetaDefender's database, ABR can optionally upload the full file for a live multi-engine scan. The checksum lookup and block all happen transparently: the end user sees a brief "scanning" notice, and in the vast majority of cases the verdict arrives so fast there is no perceptible delay. *Malware detection* applies to both *Run As Admin* and *Admin Session* elevation types, and is available on Windows and macOS.
What problem does it solve?
When ABR removes standing admin rights from endpoints, it solves the lateral movement and privilege abuse problem - but it does not, by itself, prevent a user from requesting elevation to run a malicious file. A user might find a "free PDF converter" or a "system cleaner" online, download it, and submit it for elevation. If the organization's endpoint antivirus doesn't catch it, that elevation request could succeed and deliver malware with full administrator privileges.
*Malware detection* closes this gap. Rather than relying on a single endpoint antivirus product, ABR routes every elevation request through a cloud service that runs 30+ independent scanning engines against the file simultaneously. No single antivirus product has perfect detection; the multi-engine approach substantially increases the probability of catching a threat that one product would miss. Real-world tests documented in ABR's own knowledge base show files that passed Windows Defender on the endpoint but were caught by MetaDefender.
There is an important secondary benefit: knowing that every elevated file is scanned by 30+ engines makes it reasonable to operate in auto-approval mode (without *Require Approval*) for most elevation types. The malware check provides a floor of protection even when no human approver reviews individual requests. ABR's own documentation takes this position directly - describing the combination of malware scanning plus auto-approval as sufficient for many organizations.
Every elevation, scanned by 30+ engines in under 0.1s
ABR sends each file's SHA-256 to OPSWAT MetaDefender. If any major engine - or two of any kind - flags it, execution is blocked on the endpoint.